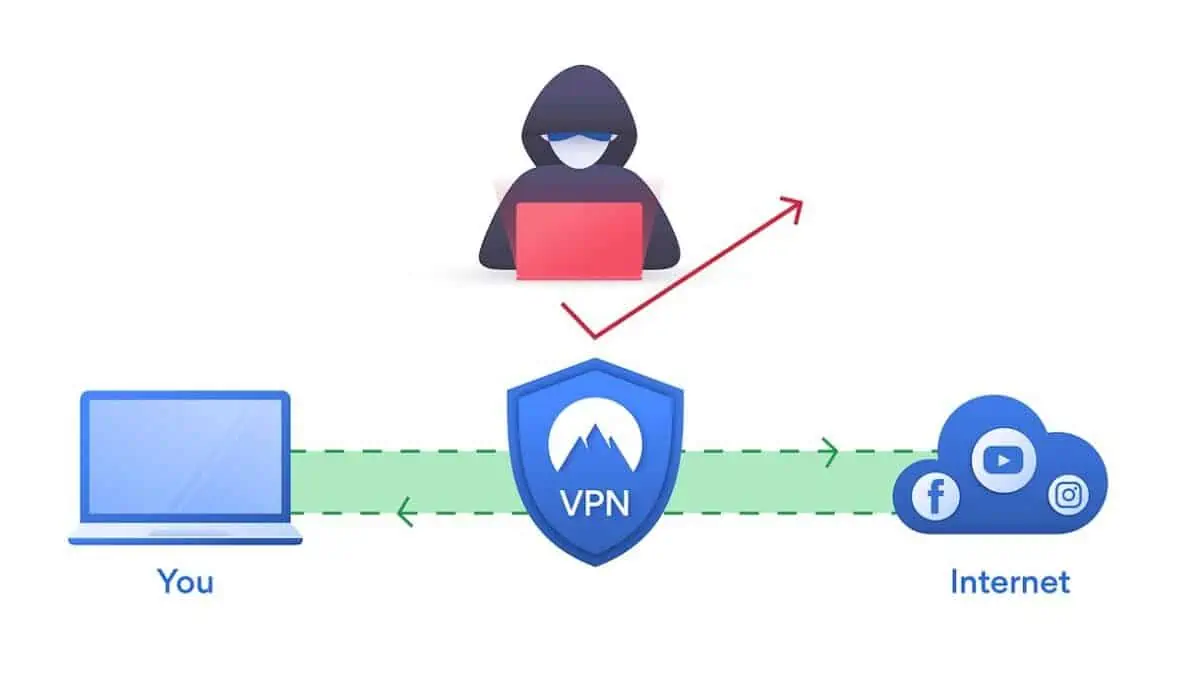
We all know how important cybersecurity is now that technology powers commerce in such a significant way. But if you perform work as part of a supply chain, you know that the stakes are especially high with cyber security the weakest link.
Given that you’re part of a network of providers, vendors, transporters and managers, the impact of the weakest link in the supply chain cybersecurity “chain of custody” can be significant.
Continue reading “Cyber Security: The Weakest Link is Your Biggest Risk!”